Active Directory comprehensive guide, from installation and configuration to security auditing. Part 7: Understanding the AD infrastructure - Ethical hacking and penetration testing
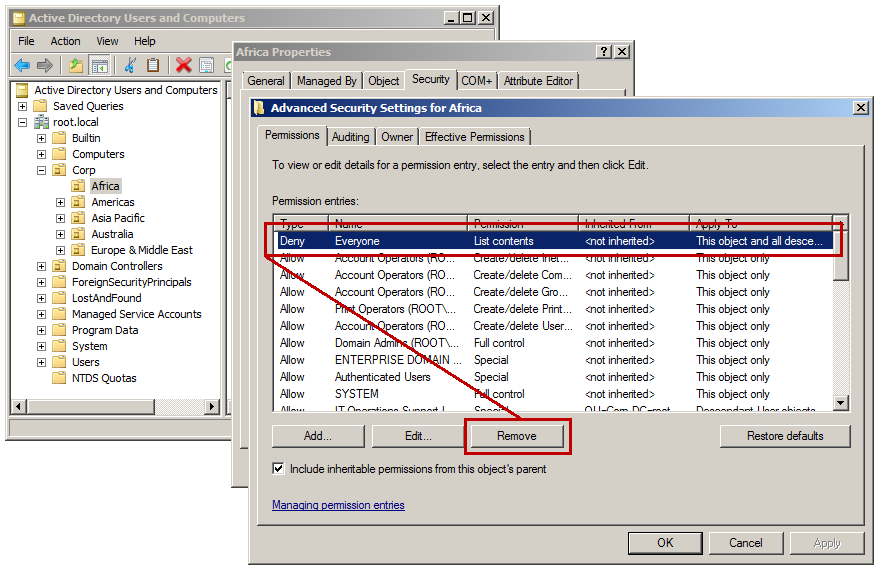
Active Directory Security Blog: How To Easily Identify & Thwart Sneaky Persistence in Active Directory
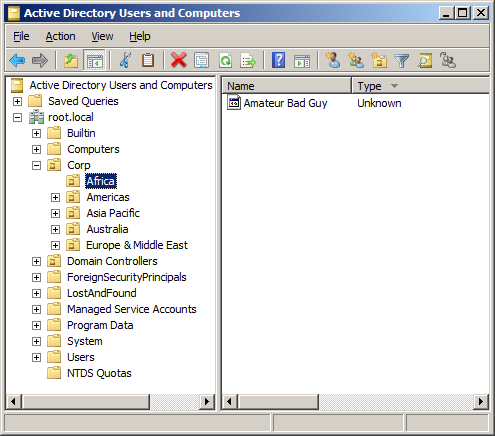
Active Directory Security Blog: How To Easily Identify & Thwart Sneaky Persistence in Active Directory
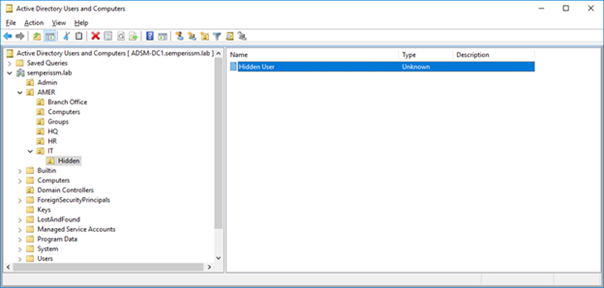
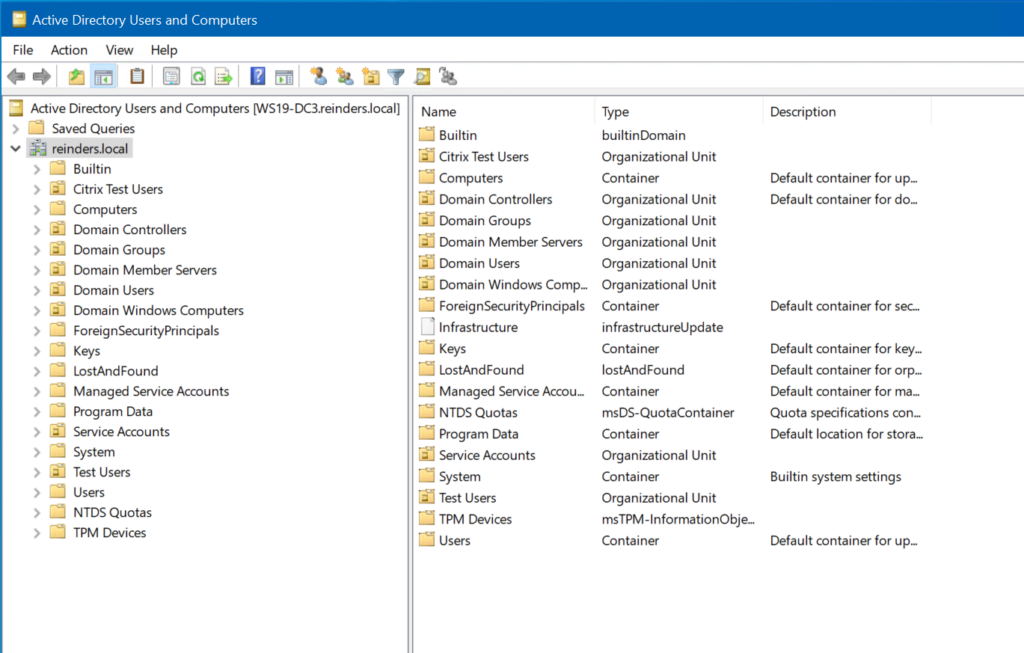
![Understanding hidden default containers - Windows Server 2019 Administration Fundamentals - Second Edition [Book] Understanding hidden default containers - Windows Server 2019 Administration Fundamentals - Second Edition [Book]](https://www.oreilly.com/api/v2/epubs/9781838550912/files/assets/87bbf395-d221-4441-8eeb-7d9228f9cb41.png)