PPT) 1 Adaptively Attribute-Hiding ( Hierarchical ) Inner Product Encryption 2012 / 4 / 18 Tatsuaki Okamoto ( NTT ), Katsuyuki Takashima ( Mitsubishi Electric - DOKUMEN.TIPS
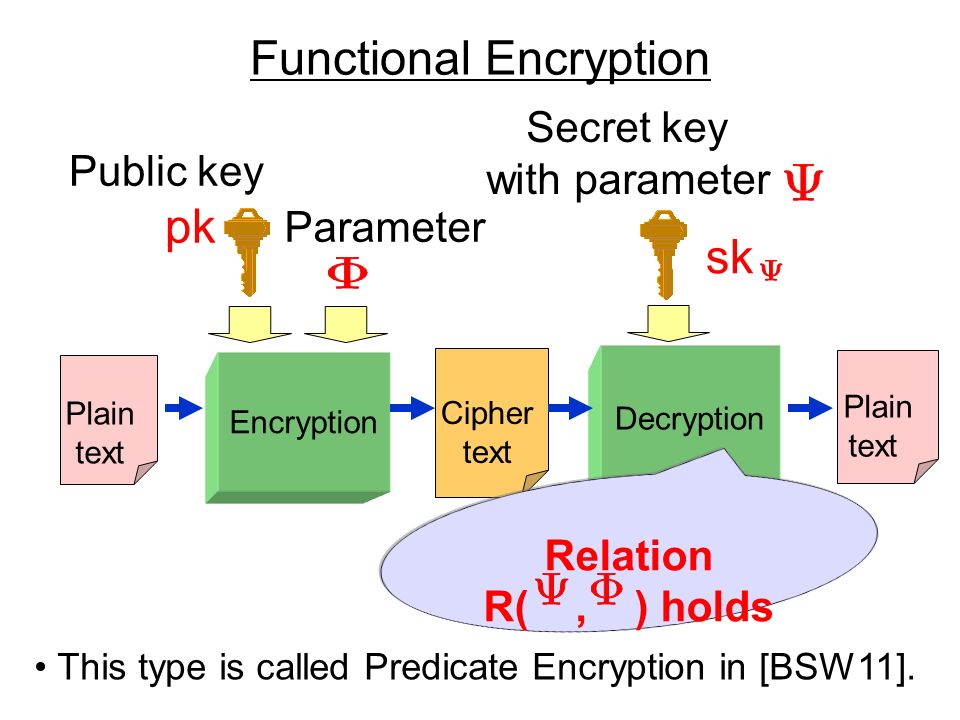
![PDF] An Efficient Cryptography-Based Access Control Using Inner-Product Proxy Re-Encryption Scheme | Semantic Scholar PDF] An Efficient Cryptography-Based Access Control Using Inner-Product Proxy Re-Encryption Scheme | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/fb79f18c0685f9786ce0ef495ff845e0ac50c142/2-Figure1-1.png)
PDF] An Efficient Cryptography-Based Access Control Using Inner-Product Proxy Re-Encryption Scheme | Semantic Scholar
2-Step Multi-Client Quadratic Functional Encryption from Decentralized Function-Hiding Inner-Product
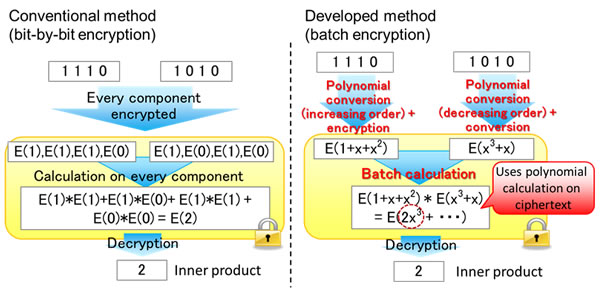
Fujitsu Develops World's First Homomorphic Encryption Technology that Enables Statistical Calculations and Biometric Authentication - Fujitsu Global

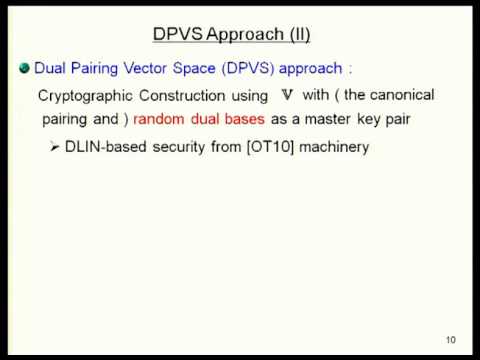
Fully Secure Functional Encryption: Attribute-Based Encryption and (Hierarchical) Inner Product Encryption Allison Lewko Tatsuaki Okamoto Amit Sahai The. - ppt video online download

Fully Secure Functional Encryption: Attribute-Based Encryption and (Hierarchical) Inner Product Encryption Allison Lewko Tatsuaki Okamoto Amit Sahai The. - ppt video online download

Multi Input Functional Encryption for Inner Products Function Hiding Realizations and Constructions - YouTube
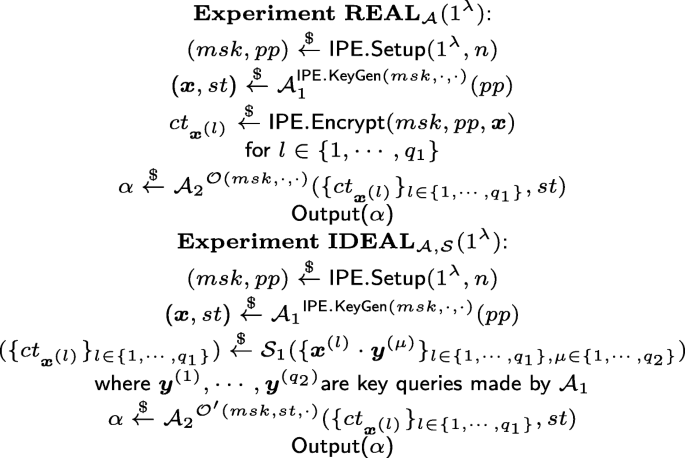
Efficient functional encryption for inner product with simulation-based security | Cybersecurity | Full Text

![PDF] Functional encryption for inner-product evaluations | Semantic Scholar PDF] Functional encryption for inner-product evaluations | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/40f98cf0dcac4be854d52a0f30febd042ee25a22/33-Figure3.1-1.png)